|
[VIEWED 6686
TIMES]
|
SAVE! for ease of future access.
|
|
|
|
atit

Please log in to subscribe to atit's postings.
Posted on 10-31-07 9:41
AM
Reply
[Subscribe]
|
Login in to Rate this Post:
0  ?
? 
|
| |
Hello all,
I need to monitor packets for my project and i would appreciate any help i receive. I am doint a client server program in java using sockets. All i want to do is monitor the communication between them. Also if possible i want to see what data is being sent and receive. Further would be to take that data and see if the reply attack can be performed.
But right now i couldn't do anything. I tried ethereal to monitor what's going on. I unhooked my internet connection before i ran the program to have less noise. Wheni run the program i have client interacting with the server and receiving and sending information. But the ethereal show's nothing.
Am i missing something here?
Any Help.?
|
| |
|
|
|
|
Bob Marley
Please log in to subscribe to Bob Marley's postings.
Posted on 10-31-07 10:49
AM
Reply
[Subscribe]
|
Login in to Rate this Post:
0  ?
? 
|
| |
bro/sis
don't force yourself to be a computer engineer if you're not made for it/if you lack the intellectual skills. You might be happier/better off in some other field. You know you have the choice and please do not follow the social pressure like in Nepal. Doctors,engineers an pilot, now it's computer engineer. No offence.
|
| |
|
|
oldmaven

Please log in to subscribe to oldmaven's postings.
Posted on 10-31-07 10:53
AM
Reply
[Subscribe]
|
Login in to Rate this Post:
0  ?
? 
|
| |
. Seems to me you arent listening on the "right" interface in ethereal. Check that out! You might want to use windump as well for such purposes , if you dont want ethereal hassles.
|
| |
|
|
atit

Please log in to subscribe to atit's postings.
Posted on 10-31-07 2:28
PM
Reply
[Subscribe]
|
Login in to Rate this Post:
0  ?
? 
|
| |
Well i belive i am not listening on righ interface. As there is nothing listed as soon as i unplug the cable.
I searched internet for ways to monitor packets in localhost but couldn't really implement them. Now i am trying to get a network by hooking up to a router. So i have a laptop running the client side of the code and desktop with mysql and apache (Xampp) running the server side. Now to connect from laptop to desktop i would use 192.168.1.103 instead of localhost. Connection works successfully. I could run ethereal to collect data. But there is a lot of info I could hardly differentiate the packets generated by my laptop.
Thanks bob for your concern, but for me its too late to pull out. Help is higly appreciate.
|
| |
|
|
oldmaven

Please log in to subscribe to oldmaven's postings.
Posted on 10-31-07 3:31
PM
Reply
[Subscribe]
|
Login in to Rate this Post:
0  ?
? 
|
| |
. You could listen without segregating the server . i.e on the localhost as well. Just had to make sure, you listen on the "right" interface. Nevertheless, since you've already done that : Now all you need to do is to sniff the "right" data. : ) Capture Filter is how you do that! First , see which port your application listens to, and filter on that port. You may even color them or discard other packets to see the clean shit "right" data.
Last edited: 31-Oct-07 03:31 PM
|
| |
|
|
atit

Please log in to subscribe to atit's postings.
Posted on 10-31-07 7:08
PM
Reply
[Subscribe]
|
Login in to Rate this Post:
0  ?
? 
|
| |
sorry could not check your reply on time.. i had to disconnect internet and time flew by. Yeah i am connecting to port 9999 so let me try what you've just told me.. let me disconnect and be back soon. :p
|
| |
|
|
atit

Please log in to subscribe to atit's postings.
Posted on 10-31-07 7:41
PM
Reply
[Subscribe]
|
Login in to Rate this Post:
0  ?
? 
|
| |
0000 00 11 11 be fc 02 00 16 6f 5c 70 92 08 00 45 00 ........ o\p...E.
0010 00 66 3a 75 40 00 80 06 3c 01 c0 a8 01 64 c0 a8 .f:u@... <....d..
0020 01 67 09 f3 27 0f 4e f5 f6 b2 59 3d c4 c3 50 18 .g..'.N. ..Y=..P.
0030 44 e8 94 7d 00 00 78 78 78 78 78 78 40 68 6f 74 D..}..xx xxxx@hot
0040 6d 61 69 6c 2e 63 6f 6d 0d 0a 32 30 34 30 33 36 mail.com ..204036
0050 61 31 65 66 36 65 37 33 36 30 65 35 33 36 33 30 a1ef6e73 60e53630
0060 30 65 61 37 38 63 36 61 65 62 34 61 39 33 33 33 0ea78c6a eb4a9333
0070 64 64 0d 0a dd..
Thanks for your Help Oldmaven, red is the username and green the hashed password. You are my man . I wish i could assign you 10 duke points.
Happy Tihar.
I'll post here if i have some more problem on packet sniffing.
|
| |
|
|
Saajha

Please log in to subscribe to Saajha's postings.
Posted on 10-31-07 8:29
PM
Reply
[Subscribe]
|
Login in to Rate this Post:
0  ?
? 
|
| |
Awesome ... so you could sniff your traffic and was able to see your cleartext hotmail userID eh~
Ethereal/Wireshark is great.. ain't it?
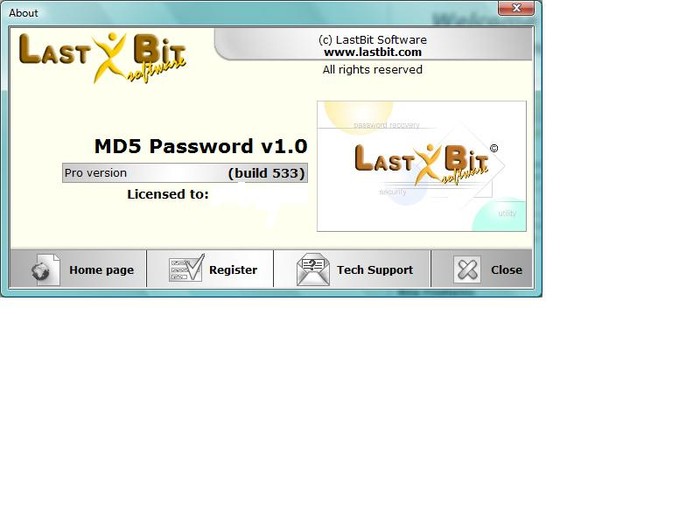
BTW, giving out MD5 hash is risky. It can be reverse bruteforced.
@oldmaven, you seem to be fairly familiar with packet analysis - are you into IDS as well?
~@~
|
| |
|
|
atit

Please log in to subscribe to atit's postings.
Posted on 10-31-07 9:57
PM
Reply
[Subscribe]
|
Login in to Rate this Post:
0  ?
? 
|
| |
I am starting to like this.
Well about the reverse bruteforce, which one is highly resistant sha-1 or md5?
Since high-tech people are here let me pop this question. How do you do a DoS?
I want to flood the server (so that it could not serve). This will only be deployed on my machine 
Any other, better, cheaper and easier means to do this?
|
| |
|
|
DC_virus

Please log in to subscribe to DC_virus's postings.
Posted on 10-31-07 10:07
PM
Reply
[Subscribe]
|
Login in to Rate this Post:
0  ?
? 
|
| |
are you talking about reverse brutefors for sha-1 or md5 ????? is that possible??? I thought it was not possible for current available processing power to reverse brute force a MD5 ??
|
| |
|
|
Grace_S

Please log in to subscribe to Grace_S's postings.
Posted on 11-01-07 12:38
AM
Reply
[Subscribe]
|
Login in to Rate this Post:
0  ?
? 
|
| |
Interesting topic to be brought upon!
Ethereal/Wireshark is a neat sofrware and seeing all the responses I should have brought a topic on "cracking WEP", with which had a rough time not long ago.
G'luck atit!
|
| |
|
|
atit

Please log in to subscribe to atit's postings.
Posted on 11-01-07 11:16
AM
Reply
[Subscribe]
|
Login in to Rate this Post:
0  ?
? 
|
| |
So anything for Dos Attacks?? Half-open SYN-ACK
I need to flood my server, and show that there is a vulnerability using the centralized system (Single point of failure)
"cracking WEP" sounds interesting!!! So you get done with that?
|
| |
|
|
oldmaven

Please log in to subscribe to oldmaven's postings.
Posted on 11-01-07 12:02
PM
Reply
[Subscribe]
|
Login in to Rate this Post:
0  ?
? 
|
| |
. MD5 is considered not secure at all. Researches have proved there are algorithms that can actually find collisions in compression algorithmic implementation of MD5. There are claims that say they can reverse brute-force hashes as such. There are even better mechanisms to break using the "rainbow table" project that uses the time-memory trade off technique, much much faster than the brute can do. Using a "salt" value to further protect MD5 hashes is what is generally used prominent that can reduce rainbow cracks. i.e hash is md5 (password, salt)
SHA-1 is the successor for MD5. Security researchers even claim collisions on SHA-1 hash functions. LOL . I see many PGP signed messages using SHA-1 hashes. I myself signed my message on SHA-512 just in case. : ) And there has not been any collisions reported on that till date. I hope NIST comes up with great competition for us to see more interesting hash algorithms in future. @ SAAJHA, i am just a big time enthusiast. @ atit, Good that it helped you. And now you want to attack your server to prove a single point of failure. I bet there are plenty tools out there for SYN flooding. Why dont you google ? Just a small thought: if you simply run ftp server and hog the network to practically -dead- with multi connections and ingress/egress traffic, and prove that you need a back-up server ? : ) but then, i'd suggest you go for the former choice to play with the tools. @Grace_S , Cracking WEP : must be easy with so many tools available. WPA-2 is what they say should be chosen to secure your Wi-Fi , at this time. Let the time roll, and we can see wonders ahead.
|
| |
|
|
Saajha

Please log in to subscribe to Saajha's postings.
Posted on 11-01-07 4:45
PM
Reply
[Subscribe]
|
Login in to Rate this Post:
0  ?
? 
|
| |
@ dcvirus, since hashes are message digests that cannot be directly bruteforced, random strings are hashed applying the originally used algorithm, and compared against the captured hash. One of such super power tools is up there- below my previous post.
@ Grace_S, What was so rough about WEP becon cracking?
@ OldMaven, tell us about the range of your enthusiasm. I give myself 9.9 out of 10 --- about expertise ~~~ umm.. somewhere on the 3ish. :P
@ atit, What's your Server's IP address? ;)
DoS can be as simple as disconnecting the Network Cable from your NIC; to jointly hitting a single box or a cluster with thousands of Zombies (machines running bots or somehow compromised), hogging up the CPU, overflowing memory buffer, or sending tons of junk packets and clog the Network. It doesn't necessarily have to be a SYN flood. Even without a SYN and SYN/ACK (first two steps of a three-way handshake), an attacker can send a continuous stream of ACK packets to cause Denial of Service. For a standalone server (presumably your case), DoS is trivial, since there's no load balancing or failover.
~@~
|
| |
|
|
atit

Please log in to subscribe to atit's postings.
Posted on 11-01-07 9:25
PM
Reply
[Subscribe]
|
Login in to Rate this Post:
0  ?
? 
|
| |
Well i am using localhost. so it is 192.168.1.103. I am probably looking at some small piece of code that would overflow memory. Some small piece of c++ or java code that can be used. So you'd suggest i establish as many connection as possible on the socket 9999(localhost my case ) using any one of the program ?? Can that be done (?)
is there limitation to how many connection can be established on one socket ? I will search this in google too but i wanted to post this question here as well.
I see lot of room for GROWING.
|
| |
|
|
Grace_S

Please log in to subscribe to Grace_S's postings.
Posted on 11-02-07 12:21
PM
Reply
[Subscribe]
|
Login in to Rate this Post:
0  ?
? 
|
| |
Oldmaven,
I too thought cracking WEP was quite an easy task, especially with many tools available. Chose BackTrack2 but somehow was unable to crack, probably because of peer pressure of other classes too.
Saajha and atit,
Couldn't crack the password, nevertheless was such a facinating experience. Technology can do so much!
Best regards
|
| |
